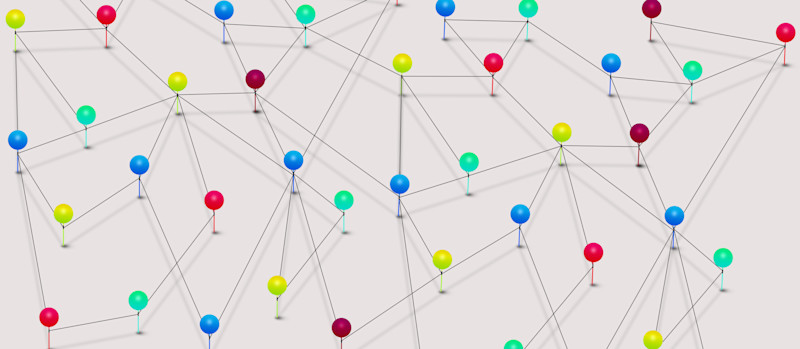
One of the first steps that a company should consider when building or enhancing their cybersecurity plan is to map out all access points to the company’s systems and network, including the points of interaction between various systems within and outside the network. This task should be completed whether a company’s internal resources will be responsible for implementing the security plan or if these services are contracted with an outside organization.
This interaction map has two primary functions: (1) Define every point of vulnerability to your business systems; (2) Provide a clear path for deploying appropriate security functions to address each of these points of vulnerability. This map should be a living document capturing changes that may introduce new points of vulnerability or new interactions between systems that may require implementation of additional security functions.
The specific tool used to create the interaction map is not overly important – this will depend on the complexity of your network structure and the familiarity within your organization with various mapping tools. The key is to do the mapping and to keep it up to date – make it the working document upon which you build your overall cybersecurity plan.
When building the interaction map, it is not necessary to define every individual piece of equipment. For example, if there are 10 similar computers and users in the manufacturing operations office that all have similar capabilities and access rights to business systems, these can be grouped into a single class. Another example may be visitors who are granted access to your network or systems – these too can be mapped as a class if they have equal access and rights. When grouping interfaces into classes, it is important to assure that all security functions applicable to a class of equipment/users is applied to all.
The map should not only include computers, production equipment, and other devices directly connected to the business’s network; it should also include any other interface those devices have to other devices or systems outside the network. For example, all removable storage devices associated with computers or other pieces of equipment attached to the network should be mapped as additional points of vulnerability. Likewise, any devices that are owned by the company, visitors, vendors, personnel, etc. which may be temporarily connected directly to the network or connected to any device that is then connected to the network (e.g., a maintenance or service provider’s computer connected to a piece of production equipment) should also be included in the interaction map, along with any additional interfaces available to those devices. As you can see, this interaction map can get quite complex, but each of these access points is a point of vulnerability to the security of your business systems.
Another set of interfaces to be addressed in the interaction map are the interfaces between business systems and from business systems to databases/mass storage systems. This includes interfaces to resources both within the company or connected through the internet (or other remote connection). The importance of providing security functions for interfaces to resources outside the company are pretty clear. Consideration of the interface interactions between systems within the company are often overlooked. Defining these interfaces, limiting those interfaces, and deploying security functions to these interfaces are important to minimize the spread of a security threat across systems. Such security breaches can interrupt broad sectors of a business. Additionally, adding these security measures can minimize the potential for a “backdoor” security breach where multiple systems can be compromised once any one system is penetrated.
Once you have a clear picture of all points of vulnerability to your business systems, you now have a platform upon which to build the balance of your cybersecurity plan.
For more on this topic, we invite you to explore the Building an Advanced Cybersecurity Plan article series.
Part 1: Engagement and Reinforcement
Part 2: Interaction Mapping
Part 3: Access Control
Part 4: Electronic Media Protection
Part 5: Identification and Authentication
Part 6: Activity Logging, Auditing, and Traceability
Part 7: Network Resource Configuration Management
Part 8: Communications, Network, and Database Security
Part 9: Personnel and Infrastructure Security
Part 10: Maintenance and Incident Response